A list of cool “features” or writing techniques that I’ve seen in papers; in the text itself, the citations, figures, etc.
Direct PDF linking. The DOI isn’t there, which isn’t great though (link could break?)
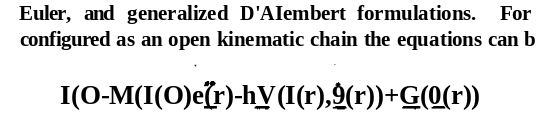
Looks like this:
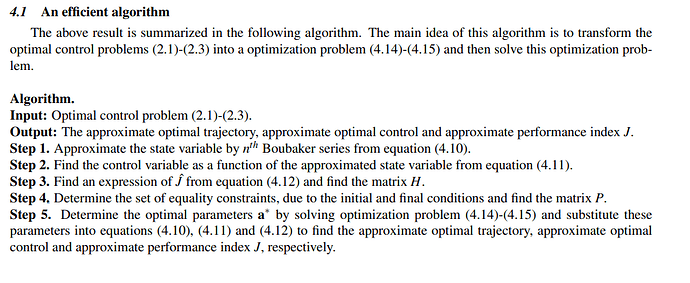
From the HamPath user guide: http://www.hampath.org/wp-content/uploads/2016/09/user_guide_hampath_V3.pdf
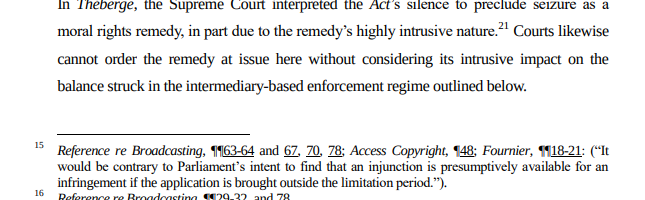
In legal documents, footcites containing quotes from the work cited
https://www.cira.ca/sites/default/files/2020-08/A-440-19_CIPPIC-CIRA_Intervener_Factum.pdf
Lin RR, Assistant R, Kascak AF, Professor A, Alexander RM. Active Control of Transient Rotordynamic Vibration of Optimal Control Methods,". 1988. doi.org/10.1.1.1052.3537
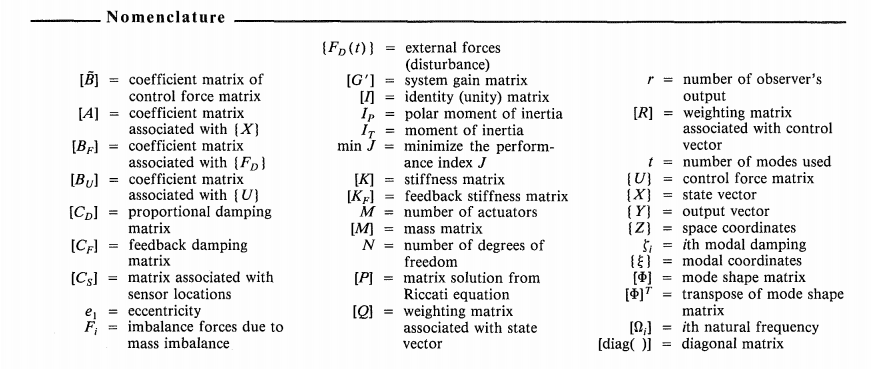
Detailed and exhaustive nomenclature. Might be improved by adding a definition for each part.
“They’re communicating to the public” sgu 832 title
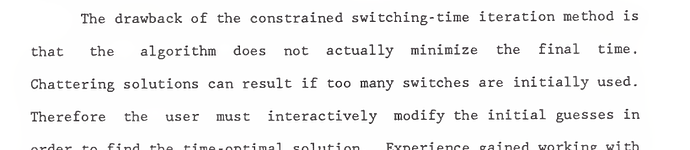
Determination of bang-bang controls for large nonlinear systems, David Donald Niemann
Has an entire chapter devoted to “conclusions and recommendations”, which also includes key drawbacks. I like this layout.
Google scholar only indexes papers (outside accepted) with explicit bibliography sections. This rules out some ‘alternative’ (bottom of page) bib styles.
10.1093/mnras/staa2487
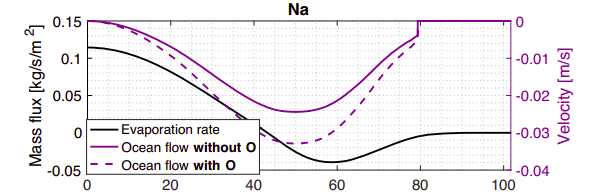
What a pleasant chart theme.
Technical abstract / plain language summary
10.1029/2021GL093880
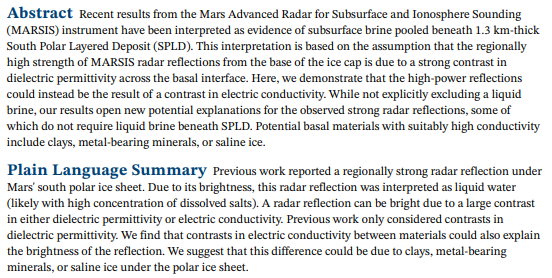
In fact, could the summary be written by other people - the reviewers, say?
One thing to keep in mind is when scanning in old documents to institutional repositories, the OCR of some scanners can completely mangle math
Darwin usually speaks in the first person plural when analyzing empirical evidence he has collected and only uses the first person singular when he is specifically speaking about his own actions, such as, “…many special facts which I have collected,” or when he is speaking about his own qualms, such as “I am well aware that there are on, on this view, many cases of difficulty, some of which I am trying to investigate.” However, when analyzing his evidence, he always uses “we”, such as “we notice”, or “we understand”(2). Darwin’s change in footing when he is explaining his theory places himself and the reader on the same level and makes him a more “humble” presenter, allowing us to suspend disbelief for at least the time being and trust him.
Add PROCESS.md with instructions on how to repeat, guidelines on validation requirements, things to watch out for, etc
add automated unit test with virtualenv to check that installation process goes without a hitch - check python version
Adding line numbers to preprints makes text difficult to select and copy. The same is true of two-panel layouts, which usually copy improperly.
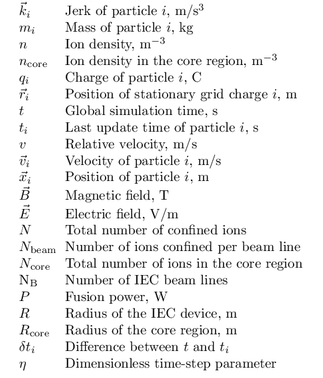
Nomenclature with units
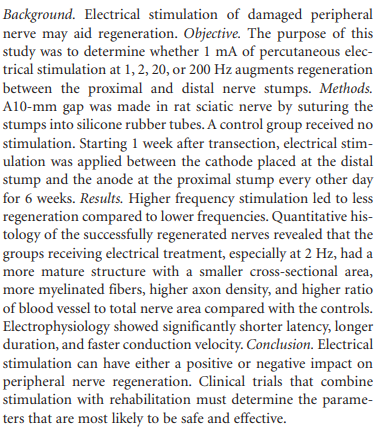
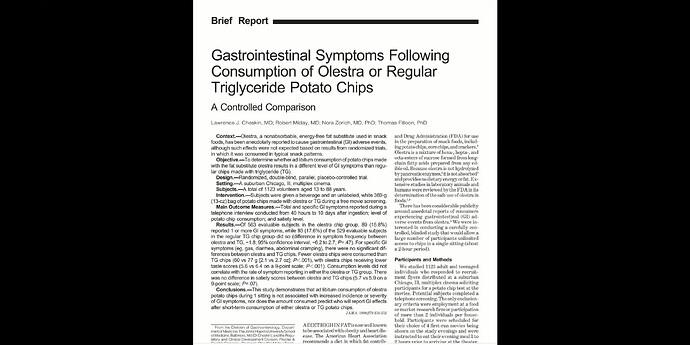
An abstract with background/objective/methods/conclusion - neat!
I’ve noticed a defect in how I write in a logbook.
Need to maintain a precise control over the nouns and verbs. It’s easy to write sentences in an ambiguous way that can’t be easily understood later. For instance:
The machine had been removed from the rack. The wire on the machine was removed. I then re-inserted it.
Which it does re-inserted refer to? This is a clunky example, but a more general problem
Better:
Machine #32, acme pulse shaper model 3352, had been removed from rack 3 and was laying on the ground. Wire 7 on the machine was not connected. D.C. then re-inserted wire 7 into socket 3.